Executive Summary
Deep analysis of SHA-2. Ekcs Data Intelligence's research database aggregated 10 expert sources and 8 visual materials. This analysis also correlates with findings on how long are sha256 hashes to provide a broader context. Unified with 8 parallel concepts to provide full context.
Everything About SHA-2
Authoritative overview of SHA-2 compiled from 2026 academic and industry sources.
SHA-2 Expert Insights
Strategic analysis of SHA-2 drawing from comprehensive 2026 intelligence feeds.
Comprehensive SHA-2 Resource
Professional research on SHA-2 aggregated from multiple verified 2026 databases.
SHA-2 In-Depth Review
Scholarly investigation into SHA-2 based on extensive 2026 data mining operations.
Visual Analysis
Data Feed: 8 Units
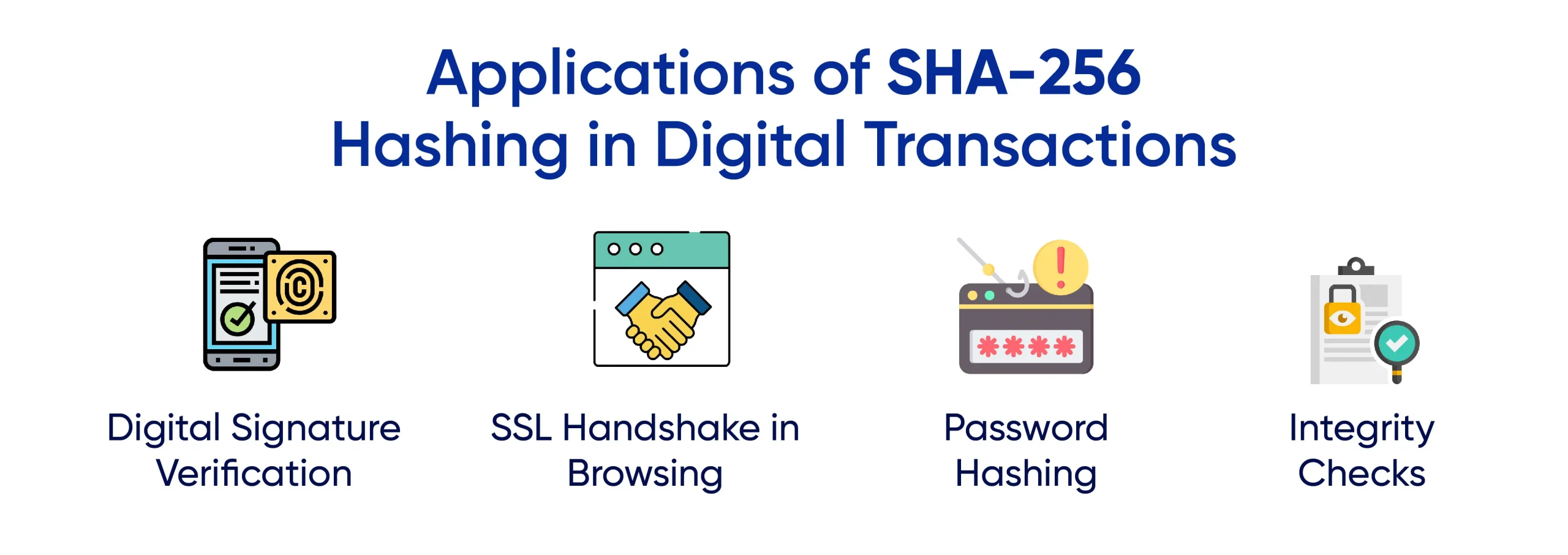
IMG_PRTCL_500 :: SHA-2
/images/image1.png)
IMG_PRTCL_501 :: SHA-2
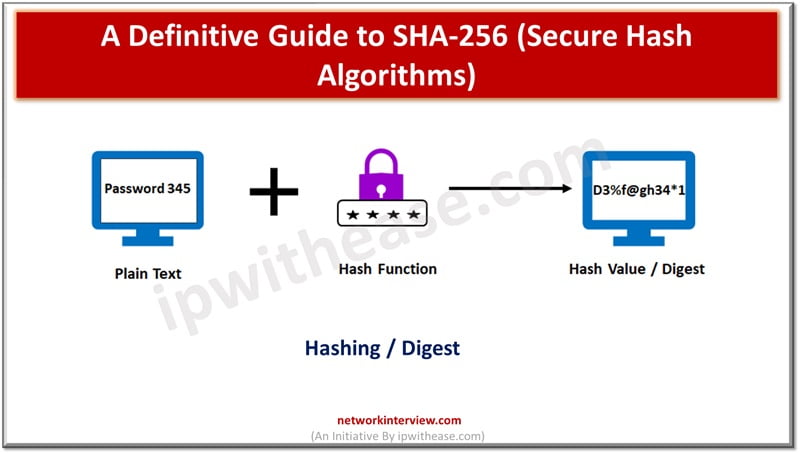
IMG_PRTCL_502 :: SHA-2

IMG_PRTCL_503 :: SHA-2

IMG_PRTCL_504 :: SHA-2

IMG_PRTCL_505 :: SHA-2
IMG_PRTCL_506 :: SHA-2
IMG_PRTCL_507 :: SHA-2
Key Findings & Research Synthesis
Research meticulous insights into what is sha256 hash used for. This intelligence node has curated 10 intelligence streams and 8 distinct images. It is correlated to 8 related topics for deeper exploration.
Helpful Intelligence?
Our neural framework utilizes your validation to refine future datasets for SHA-2.